Azure Virtual Desktop using external identities and FSlogix part 3
External Identities GA for Azure Virtual Desktop using FSlogix part 3.
Hi, welcome back! In part 2 we discussed how to setup an Azure Virtual Desktop environment for the use of an external identity. I told that there are some boundries when using this, but in the last couple of weeks a lot is happend! External Identities is not in preview anymore it's a production ready solution, ready to be used in environments. I also mentioned that one drawback was the functionality of FSlogix as it doesn't work for external identitys, but last week that's changed! It's now in public preview and ready to be used when using external identities. In this part 3 blog we are going in to the details what you need to do to set this up based on this article.
What do we need to install and configure FSlogix.
First thing I need to mention is that we don't actual need to install FSlogix, why? Because FSlogix is most of the time present already when using the Windows 11 Multi Session OS. When using other OS versions like Windows 2022 or 2025 you need to download the FSlogix software you can find this on the Microsoft website.
Most of the time you will use and configure FSlogix with configuration tooling such as Group Policy, Intune or 3th party software, for my demo I will configure the session on the host itself, but of course in production environments you need to setup a Group Policy or Configuration Profile in Intune.
Group Policy and external identity? that cannot be used in this situation, I hear you think, Yes! you are right, if you want to use External Identities with FSlogix you need to setup an cloud only environment, so you need to setup Intune or 3th party software when you want to manage and configure your FSlogix configuration.
So in this demo/blog we need to have the following resources:
- AVD sessionhosts
- Storage account with files share
- External Identity
If you want to know how to set the AVD sessionhosts up using external identities I will advice you to read part 2.
Configure the Storage Account.
In this demo/blog I will create an basic storage account v2 with the capabilities to create an files share, in production environments where there is a need to have a fast profile handeling you probably want to pick a higher sku with premium storage capabilities.
Of course I prefer to do set this up using Infrastructure as Code (Bicep), but for this situation there are a lot of extra things you need to configure, for example the enabling of "Microsoft Entra Kerberos" and grant access for the service principal, we will set this up using the portal but I also give some powershell and azure cli snippets that you can use.
Here is a little snippet in Bicep AVM Module you can use for the base set up if you want to deploy it using IaC.
1
2module createResourceGroup 'br/public:avm/res/resources/resource-group:0.4.1' = {
3 scope: subscription(subscriptionId)
4 name: 'rg-${deploymentGuid}'
5 params: {
6 name: 'rg-my-demo-group'
7 location: location
8 tags: 'demo-environment'
9 }
10}
11module createStorageAccount 'br/public:avm/res/storage/storage-account:0.26.2' = {
12 scope: resourceGroup(resourceGroupName)
13 name: 'stg-${deploymentGuid}'
14 params: {
15 name: 'stpoffslogixexternal'
16 skuName: 'Standard_LRS'
17 fileServices: {
18 Shares: [
19 {
20 name: 'fslogix'
21 shareQuota: 20
22 }
23 ]
24 }
25 tags: 'demo-environment'
26 }
27 dependsOn: [createResourceGroup]
28}
This will create the basic Storage Account with name stpoffslogixexternal and a fileshare named fslogix deployed in a resourcegroup, you need to change the storageaccountname to the name you prefer. If you have an existing environment you could deploy the storage account to the existing resource group.
If you want to know how to setup a deployment script and execute this bicep then I would advice you to read my blog about setting up an avd with custom image.
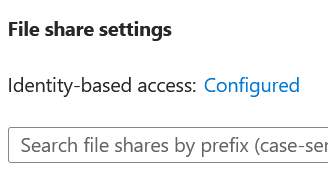
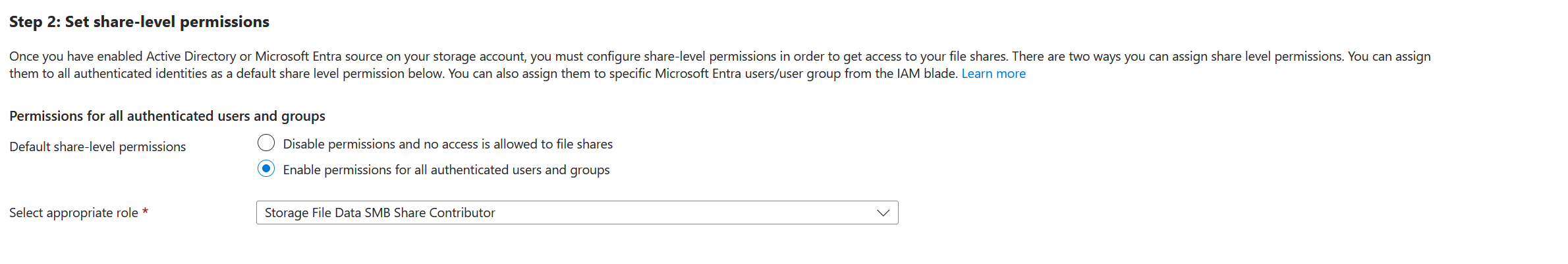
When the storage account is deployed the file share is created you can set up the "Microsoft Entra Kerberos" authentication. This can be found under the storage account -> file share below the file share settings, you will see the "not configured" clickable link:
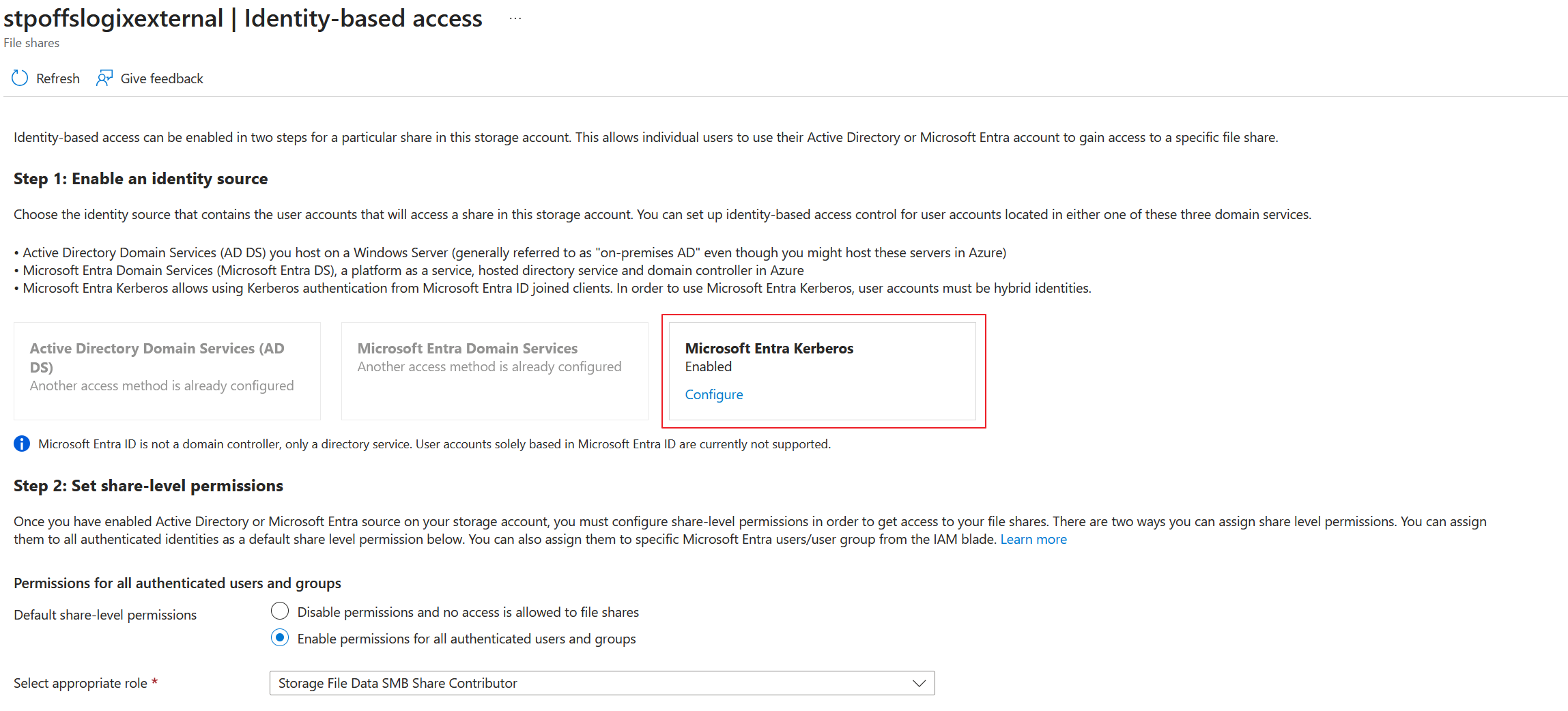
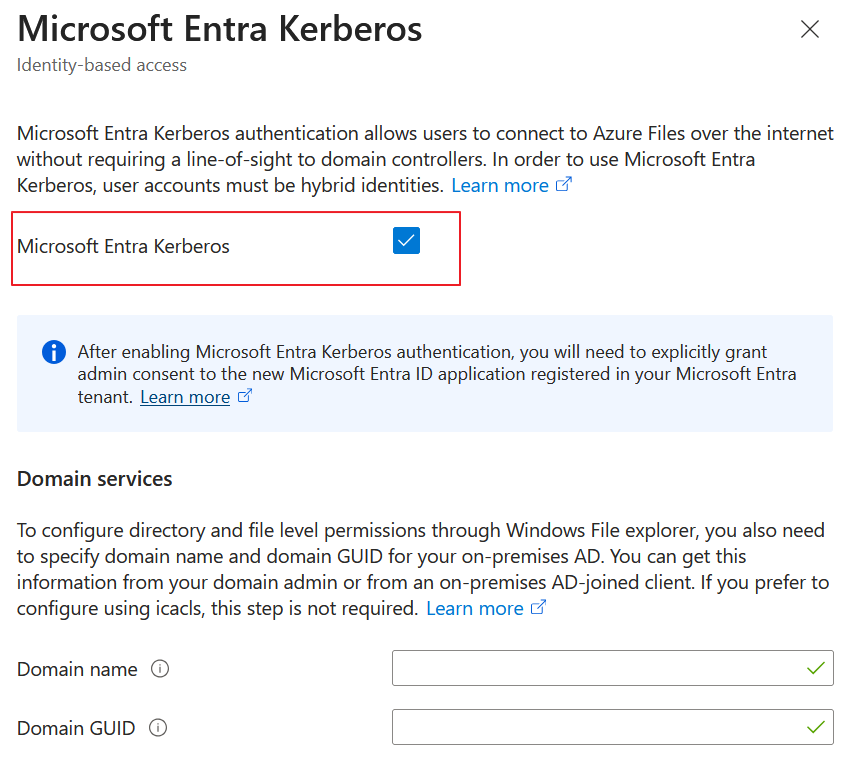
In our situation we don't need to fill in the other information based on the domain services, this is only needed when you have a dual (hybrid scenario).
If you want to enable "Microsoft Entra Kerberos" with some powershell or Azure CLI code that is possible!
powershell
Set-AzStorageAccount -ResourceGroupName <resourceGroupName> -StorageAccountName <storageAccountName> -EnableAzureActiveDirectoryKerberosForFile $true
azure cli
az storage account update --name <storageaccountname> --resource-group <resourcegroupname> --enable-files-aadkerb true
Of course you will need to login or connect using your Admin credentials and change the names in the customnames you are using. We are done setting up the storage account let's proceed to the next step.
Configure the app registration (service principal).
We have enabled the storage accounts file share to use "Microsoft Entra Kerberos" by enabling this option the resource created an app registration (service principal) in the background. We need to configure a couple of things on this app registration (service principal) for getting the authentication to work.
- Grant constent to the new service principal
The app registrion needs to have a couple of api permissions to give the identiy access to the file share, in this scenario you need to grant consent to openid, profile, and User.Read for all accounts in the directory.
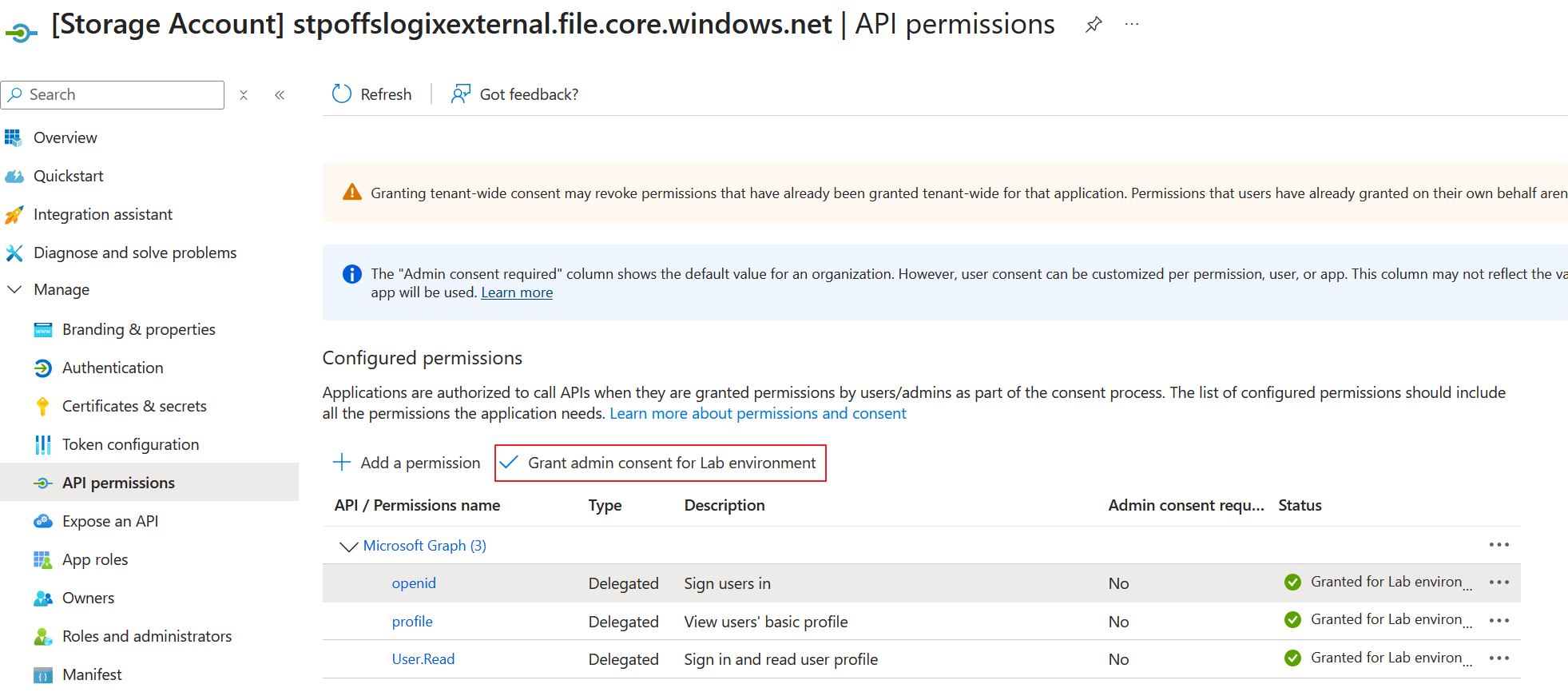
Select the 3 options and grant them the consent.
- Disable MFA for the service principal
When using a Conditional Access policy you need to disable it for this app registration, if not the authentication will not work, why? Because the identity will have an mfa (not visible) on the background when opening or writing to the fileshare.
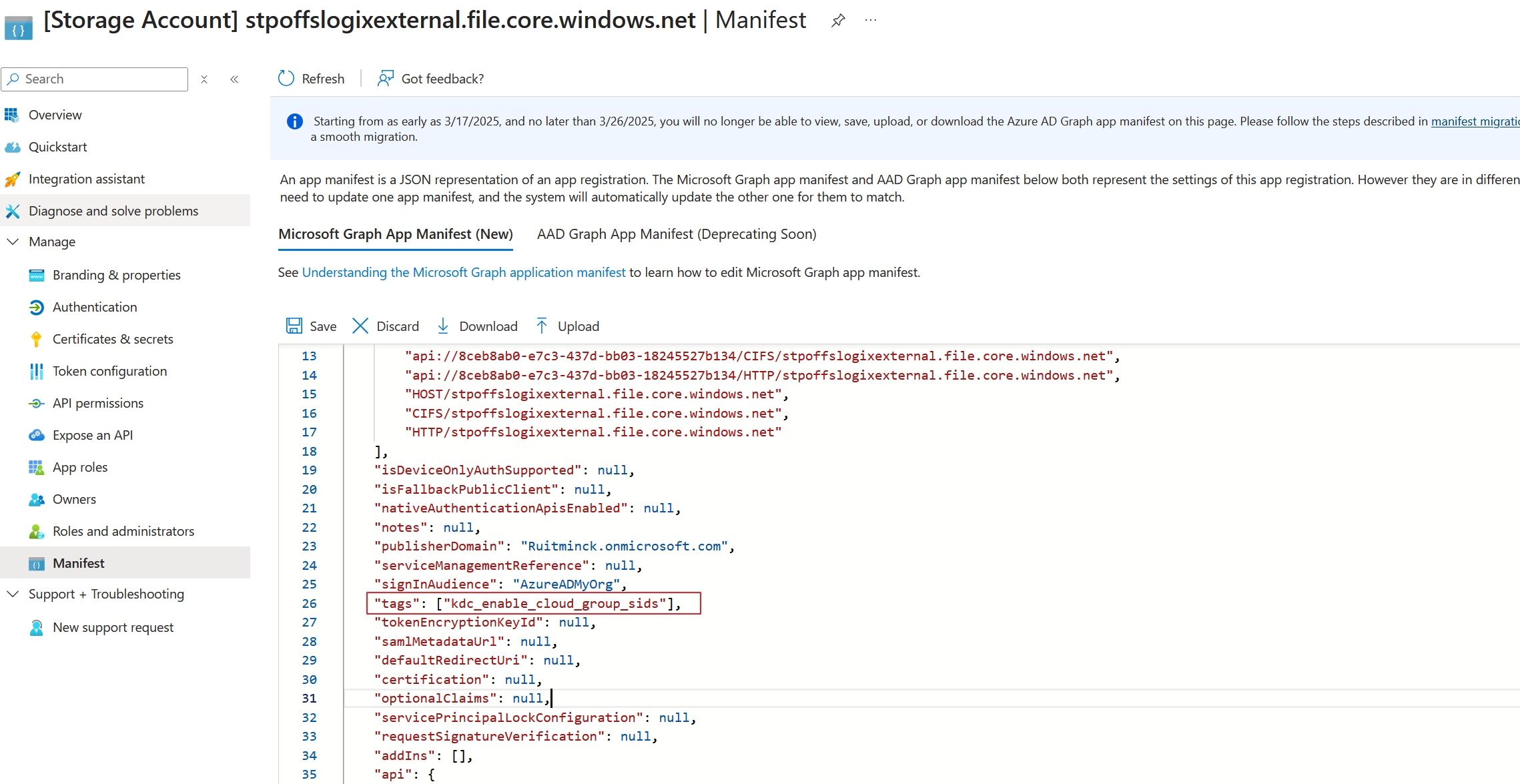
- Adding the kdc_enable_cloud_group_sids value to the manifest file
For this demo/blog it's probably not needed but certainly good to mention because with all those kerberos ticketing and group depencies you maybe bypass the 1010 windows limit, this will fix that limit.
The configuring of the app registration is done, lets proceed to the next step.
Configure the sessionhosts.
Like i said earlier in this blog, you want to use Intune or a 3th party solution to manage your session hosts when using this in production, but for the demo I will let you see how you can set this up manually by adding this on the host itself.
log in with your admin credentials on the sessionhosts and open a elevated powershell prompt.
powershell reg add HKLM\SYSTEM\CurrentControlSet\Control\Lsa\Kerberos\Parameters /v CloudKerberosTicketRetrievalEnabled /t REG_DWORD /d 1
It will now opens the way to receive kerberos tickets, you still need to restart the server because the change is not an instance change, reboot is required.
If you want to enable it using Intune please use the Settings Catalog instead of the OMA-URI method. The OMA-URI method does not work on Azure Virtual Desktop (AVD) multi-session devices. AVD multi-session is a common deployment scenario for Entra Kerberos with hybrid identities, including configurations involving Entra ID Join, FSLogix, and Azure Files.
Now that you have added the key and rebooted the server you can add the fslogix settings as well in the registry, you can use powershell for this as well, when added you need to restart the server.
1$VHDLocations = "\\yourstorageaccountname.file.core.windows.net\fslogix"
2New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name Enabled -PropertyType dword -Value 1 -Force
3New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name DeleteLocalProfileWhenVHDShouldApply -PropertyType dword -Value 1 -Force
4New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name FlipFlopProfileDirectoryName -PropertyType dword -Value 1 -Force
5New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name LockedRetryCount -PropertyType dword -Value 3 -Force
6New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name LockedRetryInterval -PropertyType dword -Value 15 -Force
7New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name ProfileType -PropertyType dword -Value 0 -Force
8New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name ReAttachIntervalSeconds -PropertyType dword -Value 15 -Force
9New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name ReAttachRetryCount -PropertyType dword -Value 3 -Force
10New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name SizeInMBs -PropertyType dword -Value 30000 -Force
11New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name VHDLocations -PropertyType string -value $VHDLocations -Force
12New-ItemProperty -Path HKLM:\SOFTWARE\FSLogix\Profiles\ -Name VolumeType -PropertyType string -Value vhdx -Force
Test the solution.
Ok when you are finished you can use the external identity to test the functionality, login using the guest account you have invited in the earlier blogs. If you have configured everything correctly you will not see hanging fslogix services or error messages when logging in or out. To check the storage account you shall see the name of the external identity in your storage acccount as well with an accurate timestamp.
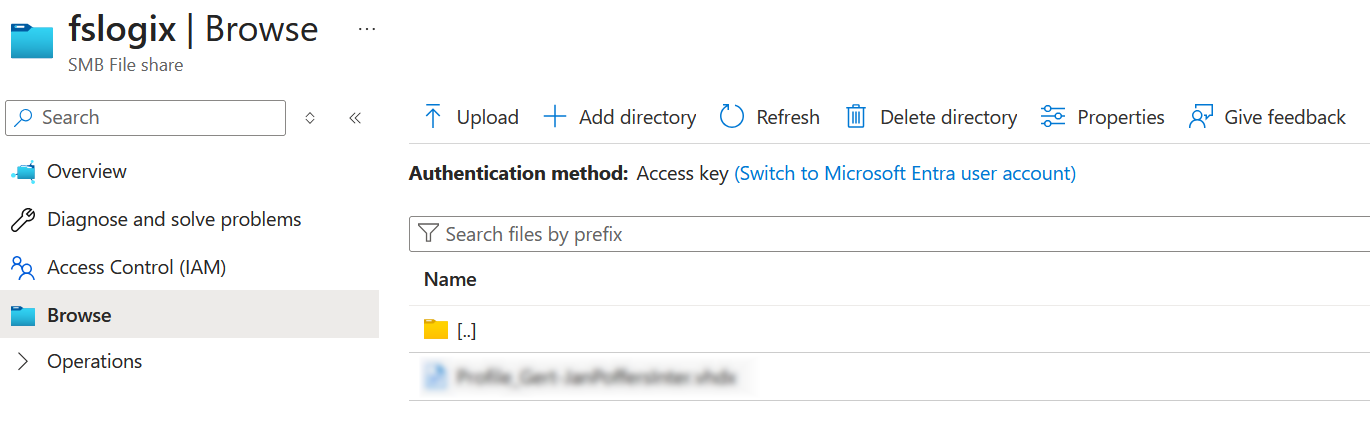
As you can see we have an working fslogix from an external identity! Of course there are a lot of extra things that can be configured when using this in production environments, you can read this in the Microsoft documentation.
Wrapping this blog series up.
So this is the end of this series blog posts regarding the use of External Identities in the Azure Virtual Desktop landscape. When I started this blog series this functionality was only in public preview where FSlogix wasn't even supported. But now the External Identities is going live and FSlogix is in public preview, how cool is that!
This new options we have for enabling External Identities really opens a door to new solutions, especially when we could use the functionality of FSlogix. Because this also opens the door for the use of Azure File Shares in general when working with External Identities.
I hope you had fun reading this blogpost, if you have question reach out and hope to see you next time!